Assignment 1: Vulnerability Assessment
Perform a Vulnerability Assessment of your place of employment or living area
Topic: Perform a Vulnerability Assessment of your place of employment or living area. If you use your work area make sure you inform the Security Manager to get permission as to what you are doing. If you live in a gated community inform the security guard of your activities.
For this assignment: The 4 Heading-1s are required. Each Heading-1 must have at least 3 Heading-2s. Each Heading must have at least 2 properly formatted paragraphs with 3 properly formatted sentences each.
NOTE: This is a Physical Security subject and the course is ISOL-634-B05.
It should include below headings:
Natural Surveillance
Territorial Reinforcement
Access Control
Maintenance
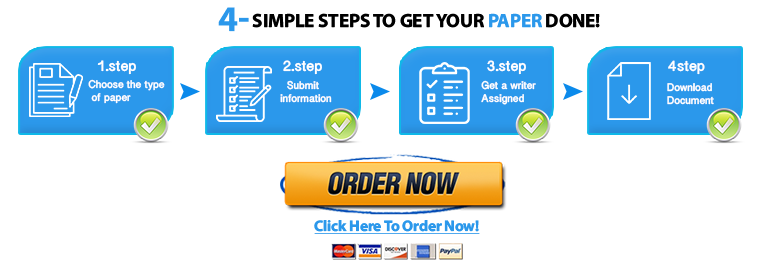
Place your order now for a similar assignment and get fast, cheap and best quality work written by our expert level assignment writers. Use Coupon: NEW30 to Get 30% OFF Your First Order
Use Coupon: NEW30 to Get 30% OFF Your First Order

How is Vulnerability Assessment Performed?
Learn about vulnerability assessment and how it is performed to ensure the security and protection of your digital assets. This comprehensive guide provides insights into the process, tools, and best practices.
Introduction
In today’s digital age, where cyber threats are ever-evolving, ensuring the security of your digital assets is of paramount importance. Vulnerability assessment is a crucial process that helps identify weaknesses and potential security gaps in a system, network, or application. By conducting regular vulnerability assessments, organizations can proactively safeguard their sensitive data and prevent unauthorized access. In this comprehensive guide, we will delve into the intricacies of vulnerability assessment, exploring the tools, methodologies, and best practices to perform an effective assessment.
How is Vulnerability Assessment Performed?
Vulnerability assessment involves a systematic and meticulous approach to identify, quantify, and prioritize vulnerabilities in a target system. The process can be broken down into the following steps:
1. Scoping and Planning
The first step in performing a vulnerability assessment is defining the scope of the assessment. This involves identifying the assets, systems, or networks to be assessed. The scope may vary depending on the size and complexity of the organization. Once the scope is defined, a detailed plan is created, outlining the objectives, methodologies, and timeline for the assessment.
2. Gathering Information
To effectively assess vulnerabilities, a comprehensive understanding of the target system is essential. Gathering information about the system’s architecture, hardware, software, and network infrastructure provides valuable insights for the assessment process. This information can be obtained through interviews, documentation review, and automated scanning tools.
3. Vulnerability Identification
The core of the vulnerability assessment process is the identification of potential vulnerabilities in the target system. This is accomplished through a combination of automated vulnerability scanners and manual inspection by cybersecurity experts. Common vulnerabilities such as weak passwords, outdated software, and misconfigurations are often the primary focus.
4. Vulnerability Classification and Prioritization
Not all vulnerabilities pose an equal level of risk to an organization. Once identified, vulnerabilities are classified based on their severity and potential impact. This prioritization enables organizations to allocate resources and address critical vulnerabilities first to minimize the risk exposure.
5. Verification and Validation
After identifying vulnerabilities, it is crucial to verify and validate their existence. This involves manually testing and confirming the vulnerabilities to eliminate false positives generated by automated scanners. Validation helps ensure that the assessment results are accurate and reliable.
6. Risk Assessment
The assessed vulnerabilities are then analyzed in the context of the organization’s risk tolerance and business objectives. Risk assessment involves evaluating the potential impact of each vulnerability and the likelihood of exploitation. This step assists organizations in making informed decisions regarding risk mitigation strategies.
7. Reporting and Documentation
A comprehensive and well-structured report is essential for communicating the assessment findings to stakeholders. The report should include details about the identified vulnerabilities, their potential impact, and recommended remediation measures. Proper documentation facilitates tracking and monitoring the progress of vulnerability mitigation efforts.
8. Remediation and Follow-up
The final step in vulnerability assessment is implementing the recommended remediation measures. This process involves patching, configuration changes, or updates to mitigate the identified vulnerabilities. Continuous monitoring and periodic re-assessments ensure that new vulnerabilities are promptly identified and addressed.
Common Tools and Technologies for Vulnerability Assessment
To perform effective vulnerability assessments, cybersecurity experts rely on various tools and technologies. Here are some commonly used tools:
- Nessus: A powerful and widely-used vulnerability scanner that identifies security weaknesses across a wide range of systems and applications.
- OpenVAS: An open-source vulnerability scanner that helps detect potential threats in networks and servers.
- Nmap: A versatile network scanning tool used to identify open ports and services, aiding in vulnerability discovery.
- Metasploit: A penetration testing framework that allows cybersecurity professionals to simulate attacks and identify vulnerabilities.
- Wireshark: A network protocol analyzer used to examine packets and identify potential security issues.
Best Practices for Effective Vulnerability Assessment
Performing vulnerability assessments requires expertise and adherence to best practices. Here are some recommendations to ensure a successful assessment:
- Regular Assessments: Conduct vulnerability assessments regularly, especially after significant changes in the system or network infrastructure.
- Collaboration: Foster collaboration between IT and cybersecurity teams to ensure a comprehensive understanding of the target system.
- Stay Updated: Keep abreast of the latest threats and vulnerabilities to enhance the accuracy and relevance of assessments.
- Patch Management: Establish a robust patch management process to address vulnerabilities promptly.
- Compliance and Standards: Align vulnerability assessments with industry standards and regulatory requirements.
- Training and Awareness: Invest in training cybersecurity personnel to enhance their expertise in vulnerability assessment methodologies.
Conclusion
Vulnerability assessment is an indispensable process that empowers organizations to protect their digital assets from evolving cyber threats. By understanding the steps involved in vulnerability assessment, using appropriate tools, and adhering to best practices, organizations can enhance their security posture and mitigate potential risks effectively. Regular vulnerability assessments combined with timely remediation measures create a robust defense against cyber-attacks, safeguarding sensitive data and ensuring the continuity of business operations.
FAQs
- What is the difference between vulnerability assessment and penetration testing? Vulnerability assessment focuses on identifying and quantifying vulnerabilities in a system, while penetration testing involves actively simulating attacks to exploit these vulnerabilities and assess their impact on the system’s security.
- Is vulnerability assessment a one-time process? No, vulnerability assessment should be conducted regularly, especially when changes are made to the system, to ensure ongoing security.
- Can automated vulnerability scanners replace manual assessments? While automated scanners are efficient in identifying known vulnerabilities, manual assessments are essential to validate results, identify complex issues, and analyze the impact of vulnerabilities.
- How often should a vulnerability assessment be conducted? The frequency of vulnerability assessments depends on factors like the organization’s risk tolerance, industry regulations, and the rate of system changes. Quarterly or bi-annual assessments are common best practices.
- What happens after vulnerabilities are identified? After identifying vulnerabilities, organizations should prioritize and address them based on their severity. Remediation measures should be promptly implemented to reduce the risk of exploitation.
- Can vulnerability assessment prevent all cyber-attacks? While vulnerability assessments significantly improve security, they cannot guarantee complete prevention of cyber-attacks. They are a proactive measure to minimize the risk of breaches.
What is the purpose of performing a vulnerability assessment?
Introduction
In today’s digital landscape, where cyber threats are ever-evolving, ensuring the security of an organization’s information systems is of utmost importance. One critical aspect of cybersecurity is conducting vulnerability assessments. This article delves into the purpose and significance of performing vulnerability assessments in safeguarding businesses from potential threats.
Understanding Vulnerability Assessment
Definition and Purpose
A vulnerability assessment is a systematic process of identifying, quantifying, and prioritizing security vulnerabilities in an organization’s infrastructure, applications, and other digital assets. The primary purpose of this assessment is to proactively discover weaknesses in the system that could be exploited by cybercriminals, insiders, or malicious entities. By understanding these vulnerabilities, organizations can take necessary measures to mitigate risks effectively.
Importance of Vulnerability Assessment
Vulnerability assessments play a vital role in preventing security breaches, data theft, and unauthorized access. They help organizations stay one step ahead of cyber threats and provide an opportunity to fortify their defenses. Regular assessments assist in maintaining compliance with industry standards and regulations while ensuring a strong security posture.
Key Steps in Performing a Vulnerability Assessment
Preparing for the Assessment
Before commencing the assessment, it is essential to define the scope, objectives, and limitations. Appropriate permissions and access to the systems should be obtained, and a team of skilled professionals should be designated to conduct the assessment.
Identifying Assets and Their Value
Understanding the organization’s digital assets and their importance is crucial. Assets can range from hardware and software to sensitive data and intellectual property. Assigning a value to each asset helps prioritize the mitigation process based on potential impacts.
Identifying Potential Threats and Risks
Threat modeling involves identifying potential threats that the organization may face, such as malware, phishing attacks, or insider threats. This step helps tailor the assessment to focus on the most probable risks.
Assessing Vulnerabilities
In this step, vulnerability scanners and manual tests are employed to identify weaknesses in the system. Scanners automate the process of identifying common vulnerabilities, while manual testing allows for a deeper assessment, uncovering less common or complex issues.
Analyzing the Impact of Exploits
Understanding the potential impact of identified vulnerabilities is crucial for prioritization. Analyzing possible attack vectors helps determine which vulnerabilities pose the most significant risks to the organization.
Providing Remediation Recommendations
After identifying vulnerabilities and assessing their potential impact, the next step is to offer actionable recommendations to mitigate these risks. These recommendations may include software patches, configuration changes, or updates to security policies.
Tools and Techniques for Vulnerability Assessment
Vulnerability Scanners
Vulnerability scanners are automated tools designed to detect known vulnerabilities in systems and applications. They provide a quick and efficient way to identify common weaknesses.
Penetration Testing
Penetration testing, or ethical hacking, involves simulating real-world attacks to identify vulnerabilities that may not be evident through automated scans. This technique helps assess the effectiveness of the organization’s defenses.
Manual Testing and Verification
Manual testing involves hands-on examination of the systems to identify complex or unique vulnerabilities that automated scanners might miss. It requires skilled security professionals with an in-depth understanding of various systems and applications.
Benefits of Regular Vulnerability Assessments
Strengthening Cybersecurity
Regular vulnerability assessments significantly improve an organization’s cybersecurity posture by identifying and rectifying weaknesses before they can be exploited.
Meeting Regulatory Requirements
Many industries and sectors have specific regulations and compliance standards related to data protection and cybersecurity. Vulnerability assessments help organizations comply with these requirements.
Minimizing Business Risks
By proactively addressing vulnerabilities, organizations can reduce the risk of potential data breaches, financial losses, and reputational damage.
Compliance Checks
Vulnerability assessments also aid in ensuring compliance with industry standards and regulations. Organizations can tailor their assessments to focus on specific compliance requirements.
Challenges in Vulnerability Assessment
False Positives and Negatives
Automated scanners may sometimes generate false positives, reporting vulnerabilities that do not actually exist. Conversely, false negatives might overlook actual vulnerabilities.
Resource and Time Constraints
Conducting thorough vulnerability assessments can be time-consuming and resource-intensive, especially for large organizations with complex infrastructures.
Managing Assessment Frequency
Determining the appropriate frequency of vulnerability assessments can be challenging. Too infrequent assessments may leave vulnerabilities undetected, while too frequent assessments may strain resources.
Integrating Vulnerability Assessment into a Comprehensive Security Strategy
Vulnerability assessments should be a part of a broader security strategy that includes proactive measures, such as regular security awareness training, robust access controls, and incident response planning.
The Role of Vulnerability Assessment in Incident Response
Vulnerability assessments contribute significantly to incident response efforts. Knowledge of existing vulnerabilities enables organizations to respond promptly and effectively to incidents.
Conclusion
In conclusion, performing regular vulnerability assessments is paramount for safeguarding organizations from potential cybersecurity threats. By identifying and mitigating vulnerabilities proactively, businesses can enhance their security posture, comply with regulations, and minimize risks. Integrating vulnerability assessments into a comprehensive security strategy will bolster an organization’s ability to protect its assets, data, and reputation.
FAQs
- How often should vulnerability assessments be conducted? Vulnerability assessments should ideally be conducted at least annually. However, the frequency may vary based on the organization’s size, industry, and risk appetite.
- Can vulnerability assessments completely eliminate all security risks? While vulnerability assessments significantly reduce security risks, it is impossible to eliminate all risks entirely. Regular assessments help organizations stay vigilant and prepared for emerging threats.
- What happens if a vulnerability is discovered during an assessment? When a vulnerability is identified, organizations should promptly apply the necessary patches or implement the recommended remediation actions to mitigate the risk.
- Who should perform vulnerability assessments? Vulnerability assessments should be carried out by skilled cybersecurity professionals or teams with expertise in identifying and remediating security weaknesses.
- Can small businesses benefit from vulnerability assessments? Absolutely! Vulnerability assessments are vital for businesses of all sizes, as cyber threats can affect any organization, regardless of its scale. Regular assessments help small businesses protect their assets and customer data.
What are the types of vulnerability assessments?
Types of Vulnerability Assessments:
- Network Vulnerability Assessment: This type of assessment focuses on identifying weaknesses in an organization’s network infrastructure, including routers, switches, firewalls, and other network devices. It helps discover potential entry points for unauthorized access and data breaches.
- Application Vulnerability Assessment: Application vulnerability assessments concentrate on examining software applications, web applications, and APIs for security flaws. By identifying vulnerabilities in the code, developers can implement necessary fixes to enhance application security.
- Cloud Vulnerability Assessment: With the increasing adoption of cloud services, assessing vulnerabilities in cloud environments has become crucial. This assessment examines cloud configurations, access controls, and shared responsibilities to ensure data protection.
- Physical Security Vulnerability Assessment: This type of assessment evaluates the physical security measures in place, such as access control systems, surveillance cameras, and security personnel, to identify potential weaknesses that could compromise the organization’s physical assets.
- Wireless Network Vulnerability Assessment: Wireless networks are susceptible to security breaches, making it essential to assess their vulnerabilities. This assessment focuses on identifying potential security gaps in Wi-Fi networks and other wireless communication channels.
- Human-Based Vulnerability Assessment (Social Engineering): Human-based assessments involve simulated social engineering attacks to assess the susceptibility of employees to phishing, pretexting, or other manipulation techniques. This assessment helps improve security awareness and training.
- Database Vulnerability Assessment: This assessment targets databases, examining their security configurations, user access controls, and data encryption to ensure the protection of sensitive information stored within the databases.
- Internet of Things (IoT) Vulnerability Assessment: As IoT devices become more prevalent, assessing their vulnerabilities is critical. This evaluation aims to identify security weaknesses in connected devices and their associated networks.
- Operating System Vulnerability Assessment: Operating system vulnerability assessments focus on identifying security flaws and weaknesses in the underlying software running on servers, workstations, and other devices.
- Social Media Vulnerability Assessment: Organizations often use social media platforms for communication and marketing. This assessment looks for potential privacy, data leakage, or reputation risks associated with the organization’s social media presence.
- Third-Party Vendor Vulnerability Assessment: Many organizations rely on third-party vendors for various services. This assessment evaluates the security measures implemented by vendors to ensure they do not pose any potential risks to the organization.
- Mobile Application Vulnerability Assessment: Mobile applications are susceptible to security threats, including data breaches and unauthorized access. This assessment examines mobile apps for vulnerabilities that could compromise user data.
- IoT Device Firmware Vulnerability Assessment: This specialized assessment focuses on identifying security weaknesses in the firmware of IoT devices, which are often difficult to update or patch once deployed.
- Industrial Control Systems (ICS) Vulnerability Assessment: Industrial control systems used in critical infrastructure sectors face unique security challenges. This assessment aims to identify vulnerabilities in ICS environments to prevent potential cyber-physical attacks.
- Red Team Assessments: Red team assessments simulate real-world cyberattacks to test an organization’s defenses comprehensively. They help identify potential gaps and areas for improvement in the overall security posture.Each type of vulnerability assessment serves a specific purpose in safeguarding an organization’s digital assets and maintaining a robust cybersecurity posture.
What is vulnerability in security testing?
In security testing, a vulnerability refers to a weakness or flaw in a system, network, application, or any digital asset that could be exploited by malicious actors. These vulnerabilities pose a significant risk as they provide potential entry points for cyber-attacks, unauthorized access, data breaches, and other security breaches.
Vulnerabilities can arise from various sources, including software bugs, coding errors, misconfigurations, outdated software versions, weak passwords, and inadequate security protocols. It is essential to identify and address these vulnerabilities proactively to protect sensitive information and maintain the integrity of digital assets.
Security testing aims to uncover and assess these vulnerabilities through various methods, such as penetration testing, vulnerability scanning, and code review. By identifying and remediating vulnerabilities, organizations can strengthen their security measures, reduce the risk of cyber threats, and ensure the safety of their digital infrastructure.

I am a professional nursing assignment expert offering comprehensive academic support to university nursing students across various institutions. My services are designed to help learners manage their workload effectively while maintaining academic excellence. With years of experience in nursing research, case study writing, and evidence-based reporting, I ensure every paper is original, well-researched, and aligned with current academic standards.
My goal is to provide dependable academic assistance that enables students to focus on practical training and career growth.
Contact me today to receive expert guidance and timely, high-quality nursing assignment help tailored to your academic needs.